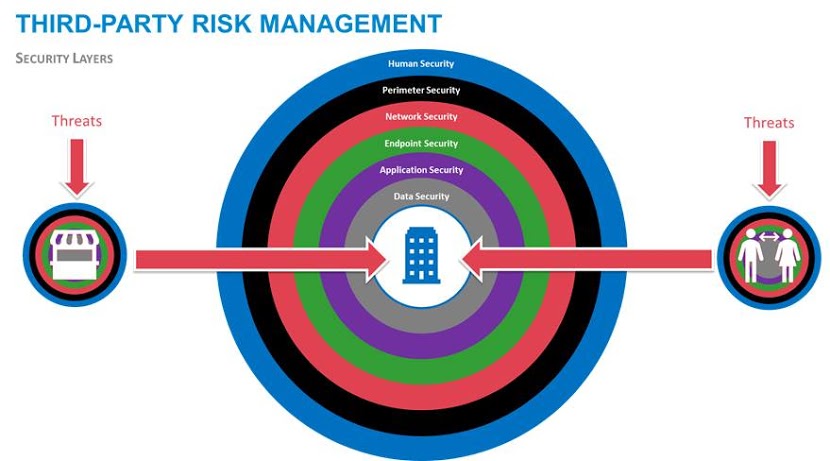
Third-party risk management is the process of managing risks that organisations are exposed to as a result of relationships with vendors, customers and other external parties. These essential relationships could endanger your organisation as you do not have control over their environments or the ability to effectively implement and manage controls to mitigate any risks.
To effectively manage the risks that third parties pose to your organisation, you should ensure that you have the following in place:
- Standardised, accurate and adequate reporting of third parties;
- Identification, tracking and logging of all third parties;
- Tools to properly and effectively manage third parties;
- Defined methods for conducting risk and other assessments; and
- Effective solutions and enterprise-wide frameworks for managing and securing third parties.
The consequences of unmanaged third-party relationships could introduce challenges ranging from faulty products from suppliers, cloud service outages and a whole host of third-party provider data breaches. Organisations are more frequently using third-party suppliers to deliver or augment their products and services, and those suppliers in turn also have third parties providing services to them. As more and more third-party products and services are used to conduct business, the frequency and impact of risk events and poor performance increases. In addition, the number, complexity and velocity of these risks also increase.
At Puleng Technologies, we have developed an all-encompassing third-party management programme that focuses on two specific elements:
- Third-party cyber security risks: This is the management and detection of third-party threats, vulnerabilities and issues, from a cyber risk perspective. Once identified, this feeds into a third-party risk management solution for further analysis and remediation. The detected threats are automatically scored and rated, and recommended actions are made available and shared with third parties for resolution.
- General third-party risk management: This includes cataloguing, management, standardisation and consolidation of third-party profiles, risks and issues, enabling performance of risk assessments, quantifications, visibility and correlation to business assets and infrastructure for the various third parties within the organisation. It allows an organisation to effectively and holistically manage its third parties.
We understand that while third-party risk management is very important as a discipline on its own, it is the cyber security risks around third parties that pose a huge challenge and massive risk for most organisations. For this reason, Puleng has chosen to give this area specific attention and to ensure it has the correct tools in place to help manage this.
Third-party risk management is one of the specific focus areas making up the greater Puleng GRC (Governance, Risk & Compliance) practice. The company’s goal and strategy is to continue to provide its customers with solutions that automate, integrate and drive higher levels of efficiencies while enforcing and mitigating risks across an organisation.
The Puleng Technologies brand continues to gather momentum and is synonymous with “project success”, technical excellence and agility. The company understands that the ability to bridge the value gap with its customers resides in its deep competency consulting, design principles and a thorough understanding of its customers’ business drivers and strategies. Puleng Technologies continues to provide its customers with technical leadership, strong returns on their investments, innovation and, above all, world-class support.
Puleng Technologies continues to push the boundaries of innovation, ready to make bold decisions on adapting its portfolio and skills in order to continue to differentiate against its competitors, while providing measurable value to its customers.
To find out how Puleng Technologies can add value to your business, give the company a call or visit the Web site at https://www.puleng.co.za/.
Yousuf Karrim [email protected].